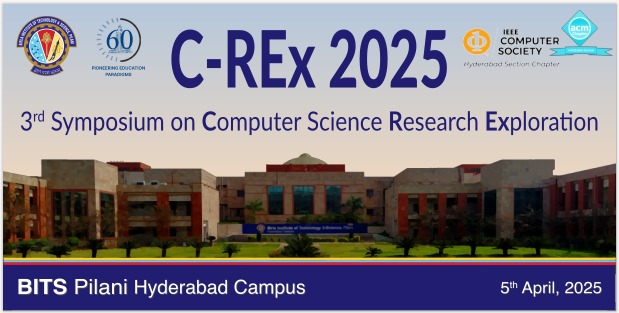
Research
The CSIS Department has faculty expertise in areas like Computer Networks, Distributed Computing Systems, Information Security, Cloud Computing, Cloud Security and Cloud Forensics, Online Social Networks, Data Privacy, Internet of Things, Blockchain Technology, Artificial Intelligence (AI), Machine Learning (ML), Databases, Data Science and Data Analytics, Computer Architecture, Cyber Security and Secure Information Systems, Information and Communication Technologies and Development (ICTD) and Human Computer Interaction (HCI), Algorithms and Computational Geometry, Natural Language Processing (NLP), Software Engineering, Theoretical & Computational Neuroscience. The department has research scholars in full time, part time as well as aspirant schemes. The full time scholars pursue their Ph.D. with funding from the Institute or from external agencies like DST, MeitY, UGC etc. The faculty members collaborate with researchers from India as well abroad. Students get funded research opportunities under several fellowships like PMRF, ASCRIN, DAAD, Viterbi-India etc.